Securing a US E-Commerce Payment Gateway
Industry: Retail & E-Commerce | Location: United States | Threat Level: High (Financial & Compliance)
The Situation: Protecting a $5M Revenue Stream
A high-volume US online retailer processing over $5 million annually was preparing to launch a completely rebuilt, custom payment gateway. Their primary concern was “Magecart” attacks—digital skimming where hackers silently inject malicious code into the checkout page to steal customer credit card details as they are typed.
If they were breached, they would not only face devastating class-action lawsuits, but payment processors like Visa and Stripe would instantly revoke their merchant accounts, permanently killing their business. They needed absolute assurance and strict PCI-DSS compliance before going live.

The Vulnerability: The Limits of Automated Scanners
The client’s internal development team had run standard, automated vulnerability scanners and assumed the code was clean. This is a fatal assumption. Automated tools look for known signatures; they cannot understand the complex logic of custom-built software.
A manual inspection was required to find the hidden backdoors that automated tools blindly skipped over.
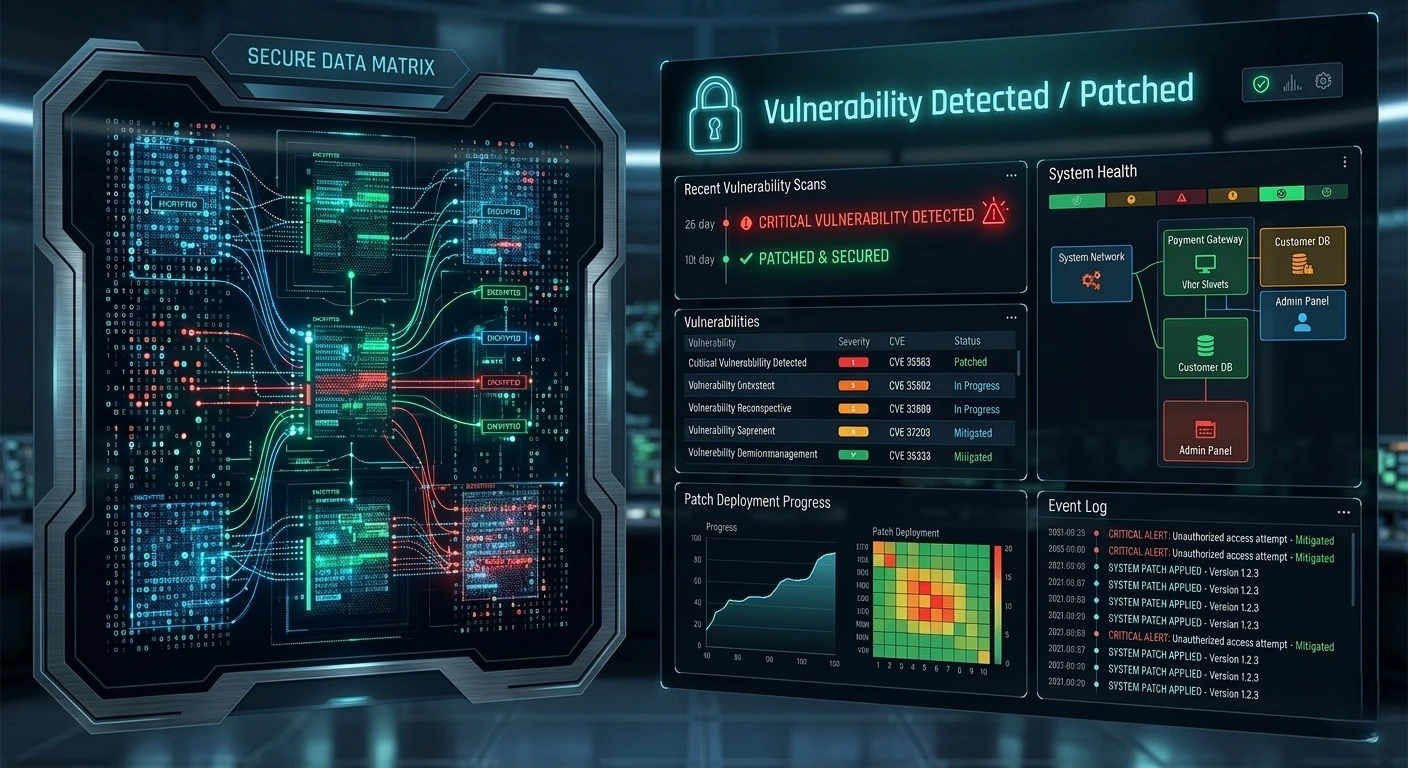
The Execution: Offensive Security Testing
Logic Edge Security was brought in to conduct an aggressive, manual Web Application Penetration Test. We attacked their staging environment exactly how a sophisticated cybercriminal would:
Reconnaissance & Mapping: We mapped the entire architecture of the new checkout flow, looking for logic flaws in how data was passed from the browser to the payment processor.
Exploitation of Custom Code: Moving entirely beyond automated scanners, our ethical hackers began manually manipulating the input fields. We discovered a critical Blind SQL Injection vulnerability buried deep within the custom database queries.
Proof of Concept: We safely demonstrated that a malicious actor could use this flaw to bypass authentication and silently siphon the entire customer database, including sensitive personal and financial records.
The Result: Launching with Ironclad Confidence
We did not just hand the client a list of problems; we gave them the exact solutions.
Remediation Roadmap: We provided the development team with specific, developer-ready code fixes to patch the SQL Injection flaw within 48 hours.
Compliance Achieved: The client successfully passed their stringent PCI-DSS audit without a single flag.
Post-Launch Security: The custom payment gateway launched on schedule and has processed millions in transactions with zero security incidents or data exfiltration.
Future-Proofing the Perimeter
E-commerce security is not a one-time event. Logic Edge was retained to implement continuous “Content Security Policies” (CSP) to block unauthorized scripts from ever loading on their checkout page, ensuring that even if a third-party plugin is compromised, the payment gateway remains untouchable.